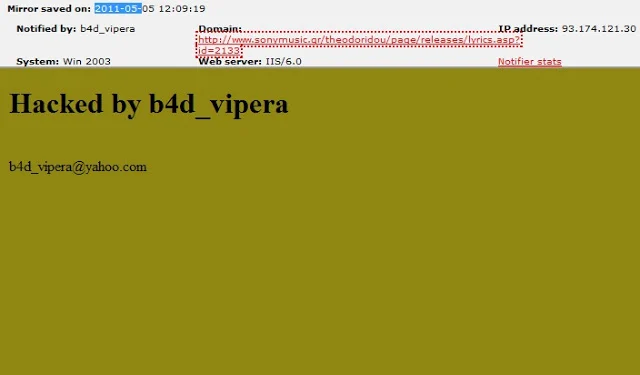
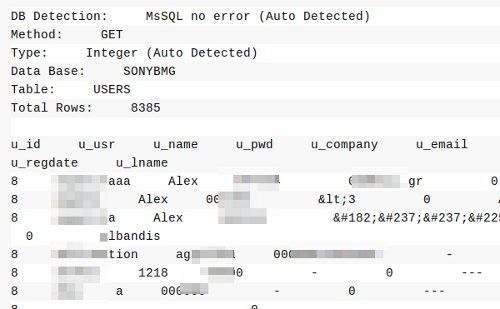
A hacker known as “b4d_vipera” recently managed to breach the website of Sony BMG in Greece, uploading a database to pastebin.com which included the real names and email addresses of users registered on SonyMusic.gr.
However, as Sophos security analyst Chester Wisniewski points out, at least some of the database appears to be incomplete, because it claims to include passwords, telephone numbers and other data that is either missing or bogus.
So, how did the hacker compromise Sony’s website this time around?
Perhaps not unsurprisingly, Vipera deployed an automated SQL injection tool.
“It’s [obviously] not something that requires a particularly skillful attacker, but simply the diligence to comb through Sony website after website until a security [vulnerability] is found,” Wisniewski explained in a blog post.
“While it’s cruel to kick someone while they’re down, when this is over, Sony may end up being one of the most secure web assets on the net. [Still], it would cost far less [for Sony] to perform thorough penetration tests than to suffer the loss of trust, fines, disclosure costs and loss of reputation these incidents have resulted in.”
The security expert also recommended SonyMusic.gr reset their passwords and remain vigilant against an inevitable wave of phishing attacks.
“Expect that any information you entered when creating your account may be in the hands of someone with malicious intent,” he warned.






