There is not a single operating system on the market that offers a plain and 100 percent bug-free experience. For mobile devices, security holds immense importance and is crucial for tech companies to make sure that everything stays private. Apple has come a long way into securing its iOS platform, which by no word is a 100 percent secure. We still see jailbreaks and bugs every now and then. However, we’re here to discuss the security level of Android with respect to the changing trends and ever-growing needs for security. Android being the most popular platform, Google is effectively working to patch all possible loopholes in terms of Android security through which hackers and users with unauthorized access can breach control of the data and other sensitive information.
We all use smartphones each day. Better, we use it all the time. We have all our personal information stored on the miniature slab of metal and glass and we regard it as ‘personal’. How personal can a device be if the manufacturer or the apps we load on it are controlled by people we do not know. Henceforth, in the growing smartphone industry, security is one of the main concerns for users as well as the tech companies.
Why Need For Android Security?
We have our credentials stored and backed up on our smartphones, our private conversations, photos, videos and everything else. Moreover, when we use apps like Facebook, we basically give all privileges to the platform to access every major part of the device, even our location, which is as personal as it can be. While companies brag and boast on all privacy concerns, regarding their supervision and conduct to keep everything private, we still hear news every now and then that a specific company stole data of millions of users without our consent. Where do we stand at this point? Apart from criticizing the companies for their doings, where can users turn to?

In terms of Android security, Google suggests that the platform is as secure as iOS and others. The platform was plagued with gigantic security gaps and now, each smartphone that Google powers is now as hard to breach as the iPhone. Whatever your stance may be in the scenario, there are certain aspects that we cannot ignore and we will be showering direct light on to them.
We Have Encountered It In The Past, We Are Encountering It Today!
As to quote some of the events which have to lead us to think what our stage is and what justifications companies are providing. Which has the potential to be some of the biggest data leaks in the past decade, talking about the latest Facebook scandal is a must. Facebook’s data leak might have actually hit more than 87 million users, where the social media giant forwarded user data to Cambridge Analytica. While it has created an uproar in the industry, Facebook is trying its best to salvage what it can through means of user control and access. Major personalities from the tech community and other as well, boycotting Facebook for breaching their security.

Apart from this, there are countless events which have led to the exploitation of user data. The exploitation does not merely require apps and they will not always ask for permissions to have access to your device. Malicious websites do it automatically, breaching the core storage of your device. Access points and links are disguised which might suggest that you’re heading in the right direction but may carry an outbreak of malicious intents to gain access to the security and permissions of your device.
Unknown Sources And Play Protect
Android is an open-source platform that deems to attract hackers into exploiting the loopholes and vulnerabilities. Even though Google Play scans an authorizes apps before putting them in the Play Store, there are certain key factors that redirect users into giving away their personal information. Moreover, there are APK files that users can side load on to their Android devices. These files come from unknown sources and might feature prerequisites that will take away your data in the long run. So it is never advised to download APK files if you’re not sure about the source or the developer.

There are two aspects that users should know of – what are the key ways of securing your Android device? Google’s efforts to minimize or eradicate unauthorized access or bypass techniques and security concerns. For the consumers, we have some points which will allow you to keep your Android security tight:
- Users should buy smartphones from vendors who release Android patches quickly. So even if there is a security risk, the update, patch or fix arrives quickly.
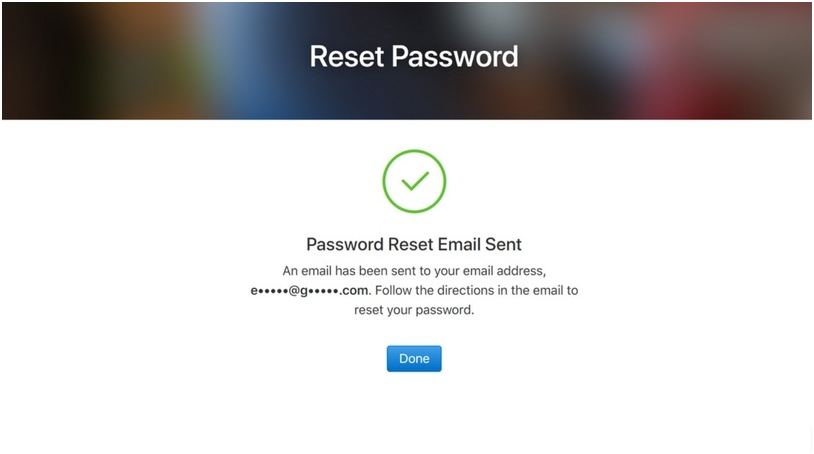
- Use two-factor authentication which will add an extra layer of protection, making it difficult for anyone to seep into your Android device.
- Install apps through the Play Store as unknown sources have the tendency to be malicious.
- Do make sure that your device is encrypted so a random stranger cannot access your files.
- Use VPN when using the Wi-Fi in public places like coffee shops etc.
- Use a strong password. The best password is alphanumeric which includes letters as well as digits and is harder to breach.
- Use of anti-virus software will allow the device to restrict malicious viruses from taking control.
- Turn off all connectivity sources when not in use.
- Uninstall apps that you do not use.
Google, on the other hand, works through its own means to provide users with a safe platform. Last year, 60.3 percent of harmful apps were detected through machine learning and that’s quite a mark. Google conducts automatic as well as manual scanning which allows for more secure apps making their way to the Play Store. More than 700,000 apps were removed from the Play Store last year that violated the store’s policy. Google’s Play Protect does not only cover the Play Store but stretches far out as well. A more proper name for the service would be Android Protect, but you get the point.
FRP – Factory Reset Protection And iCloud
Another major security concern for Android is FRP or Factory Data Protection. FRP is a security method implemented by Google to make sure that someone cannot wipe or factory reset your device when it is stolen or lost. This will make it harder for thieves to use the device. If you have FRP enabled while resetting your phone, you will have to put the right username and password of your Google account which was registered with the device.
In terms of Android security, You can still bypass FRP and your data can still be breached to some extent. This is due to the fact that are numerous security loopholes which allow individuals to get into the device without username or password. This is all thanks to third-party tools which pop up every now and then for specific versions of Android firmware. This makes the platform highly risky as your data can still be leaked without you knowing. Even though Google tends to patch these security loopholes, there are always new ones popping up every now and then.
Compared to iOS, Android security lacks behind. Take FRP for example. iOS does not feature exploits and vulnerabilities that allow for a walk around method of access. When resetting the iPhone, you will be asked to put in your Apple ID and password. Once your iPhone is reset, it cannot be accessed. This is also due to the fact that the protection of devices rely on Apple’s end as well as much as it does on an individual’s end. If you by an iCloud locked phone, the only way it can be used is through the rightful owner and his or her Apple ID and password. Apple does not allow anyone to access the phone if their phone’s iCloud is locked.
Nonetheless, Google is effectively working on improving Android security and it has gathered success. Android is less prone to malicious viruses and unauthorized access. However, Google still has a long way to go, encountering major difficulties in making the platform secure and private.
What views do you guys have on Android Security? Are there any major issues that need to be addressed? Let us know in the comments.








